What is a major use for the internet in healthcare?
The internet enables telemedicine consultations, electronic health record (EHR) access, remote patient monitoring through connected medical devices, secure provider-to-provider communication, and patient portal access for lab results and appointment scheduling. In healthcare, internet connectivity must meet strict HIPAA compliance requirements including encrypted data transmission, secure authentication protocols, network segmentation for protected health information (PHI), and comprehensive audit logging. Healthcare organizations also rely on internet connectivity for cloud-based practice management systems, medical imaging storage and retrieval, prescription management systems, and real-time insurance eligibility verification—all requiring high-availability, low-latency connections with redundant failover protection to ensure continuous patient care delivery.
What are some digital health companies?
Leading digital health companies include Teladoc Health (telemedicine platform), Epic Systems (electronic health records), Cerner (EHR and health information technology), Philips Healthcare (connected medical devices and monitoring), GE Healthcare (medical imaging and diagnostics), Medtronic (remote patient monitoring devices), Abbott (continuous glucose monitoring), and numerous specialized vendors serving telehealth, remote patient monitoring, medical device integration, health information exchange (HIE), population health management, and clinical decision support. These digital health platforms require robust cybersecurity measures including encrypted data transmission, zero-trust network access, endpoint protection for connected medical devices, HIPAA-compliant cloud hosting, comprehensive access controls, continuous security monitoring, and incident response capabilities to protect sensitive patient health information from data breaches, ransomware attacks, and unauthorized access while maintaining system availability for critical care delivery.
What is managed cybersecurity and how does it differ from traditional IT security?
Managed cybersecurity provides continuous, proactive security monitoring, threat detection, incident response, and compliance management delivered by external security experts, whereas traditional IT security relies on internal teams managing point security solutions reactively. Managed security services include 24/7 Security Operations Center (SOC) monitoring, threat intelligence analysis, vulnerability scanning, penetration testing, security information and event management (SIEM), endpoint detection and response (EDR), managed detection and response (MDR), and compliance auditing. This approach delivers enterprise-grade security capabilities without the overhead of hiring, training, and retaining specialized security personnel. For businesses in healthcare, financial services, and government contracting, managed cybersecurity ensures continuous protection against evolving threats, maintains regulatory compliance, and provides faster incident response than traditional in-house security teams can deliver.
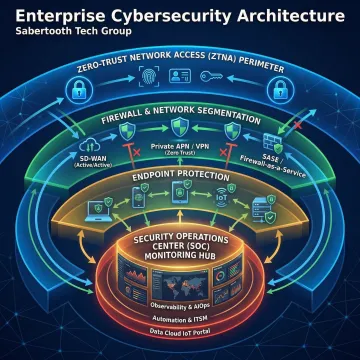
What is zero-trust security architecture and why do enterprises need it?
Zero-trust architecture operates on the principle of "never trust, always verify"—requiring authentication, authorization, and continuous security validation for every user, device, and application attempting to access network resources, regardless of location. Unlike traditional perimeter-based security models that assume internal network traffic is trustworthy, zero-trust architecture implements micro-segmentation, least-privilege access controls, multi-factor authentication (MFA), continuous monitoring, and encrypted communication for all network traffic. This approach is essential for modern enterprises supporting remote workforces, cloud applications, contractor access, and IoT devices—all of which expand the attack surface beyond traditional network perimeters. Zero-trust architecture significantly reduces breach impact by limiting lateral movement, enforcing granular access policies, and providing comprehensive visibility into all network activity, making it particularly critical for healthcare organizations handling PHI, financial institutions managing sensitive customer data, and government contractors meeting CMMC compliance requirements.
How much do managed cybersecurity services typically cost?
Managed cybersecurity service costs vary based on several factors: enterprise size (user count and device count), network complexity, compliance requirements (HIPAA, PCI-DSS, CMMC, SOC 2), threat landscape specific to your industry, security maturity level, and required service scope. Basic managed security services including SIEM monitoring, vulnerability scanning, and patch management typically start at $2,000-$5,000 monthly for small businesses, while comprehensive enterprise packages including 24/7 SOC monitoring, EDR/MDR, threat hunting, incident response, and compliance management range from $10,000-$50,000+ monthly for mid-sized to large organizations. Sabertooth Tech Group conducts a thorough security assessment, evaluates your specific risk profile and compliance obligations, then sources competitive proposals from our 300+ security provider network—ensuring you receive enterprise-grade protection at market-competitive pricing without paying for unnecessary services or features that don't address your actual threat exposure.
What compliance certifications should my cybersecurity provider have?
Your managed security provider should hold certifications demonstrating expertise in the regulatory frameworks governing your industry. For healthcare organizations, look for HIPAA compliance expertise, HITRUST certification, and experience securing electronic protected health information (ePHI). Financial services firms require providers with SOC 2 Type II certification, PCI-DSS compliance experience, and familiarity with SEC, FINRA, and GLBA requirements. Government contractors must ensure their security provider understands CMMC (Cybersecurity Maturity Model Certification) requirements, NIST 800-171 controls, and FedRAMP standards. Additional valuable certifications include ISO 27001 (information security management), Certified Information Systems Security Professional (CISSP), Certified Ethical Hacker (CEH), and GIAC Security certifications. Sabertooth Tech Group partners exclusively with security providers maintaining rigorous compliance certifications, ensuring the solutions we source meet your specific regulatory obligations and industry security standards.
How quickly can managed security services be deployed?
Deployment timelines for managed cybersecurity services vary based on organizational size, network complexity, existing security infrastructure, and scope of services. Basic security monitoring with SIEM integration typically deploys within 2-4 weeks, including initial configuration, baseline establishment, and alert tuning. Comprehensive deployments including endpoint protection rollout, zero-trust architecture implementation, network segmentation, and compliance framework alignment typically require 6-12 weeks for proper planning, phased implementation, user training, and validation testing. For enterprises with urgent security needs following incidents or audit findings, expedited deployments can sometimes be completed within 1-2 weeks for critical security controls. Sabertooth Tech Group manages the entire deployment process, coordinating between your internal IT team and selected security providers to ensure seamless implementation with minimal disruption to business operations, clearly defined success criteria, comprehensive documentation, and validated security effectiveness before cutover to production monitoring.
What should I look for in a Security Operations Center (SOC) provider?
When evaluating SOC providers, prioritize these critical capabilities: 24/7/365 monitoring coverage with redundant operations centers ensuring no security gaps during holidays or emergencies; experienced security analysts holding industry certifications (CISSP, GIAC, CEH) with demonstrated expertise in your industry's threat landscape; advanced threat detection leveraging machine learning, behavioral analysis, and threat intelligence feeds specific to your sector; defined incident response procedures with clear escalation paths, response time SLAs, and documented playbooks; comprehensive reporting providing executive summaries, detailed technical findings, compliance documentation, and actionable security recommendations; integration capabilities with your existing security tools including firewalls, endpoint protection, SIEM platforms, and identity management systems; and proven compliance expertise ensuring monitoring aligns with HIPAA, PCI-DSS, CMMC, or SOC 2 requirements. Sabertooth Tech Group evaluates SOC providers across these criteria, matching your enterprise with security partners who deliver measurable threat detection, rapid incident response, and continuous security improvement aligned with your risk tolerance and budget constraints.