SASE Implementation
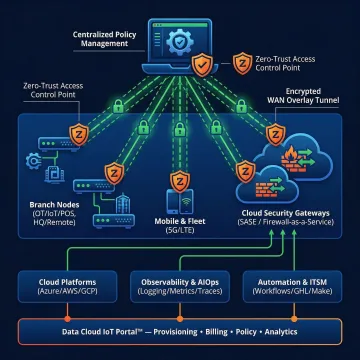
Unified SASE framework combining SD-WAN, ZTNA, CASB, SWG, and FWaaS into a single cloud-delivered security architecture with zero-trust protection and continuous threat monitoring.
As enterprises shift to SD-WAN for improved network performance and cost savings, securing distributed environments becomes mission-critical. From zero-trust frameworks and encrypted tunnels to threat intelligence integration and unified policy management, comprehensive SD-WAN security requires strategic planning across network edges, cloud on-ramps, and remote access points to protect critical infrastructure from increasingly sophisticated cyber threats.

Comprehensive security solutions designed to protect your distributed SD-WAN infrastructure from edge to cloud.
Unified SASE framework combining SD-WAN, ZTNA, CASB, SWG, and FWaaS into a single cloud-delivered security architecture with zero-trust protection and continuous threat monitoring.
Comprehensive zero-trust deployment with identity-based access controls, micro-segmentation, continuous verification, and least-privilege enforcement across your entire SD-WAN environment.
Enterprise-grade network security including next-gen firewalls, DDoS mitigation, network access control, endpoint detection and response, and SIEM platform deployment.
24/7 MDR and SOC-as-a-Service providing continuous threat monitoring, incident response, vulnerability management, and compliance reporting across distributed networks.
Secure SD-WAN implementation with application-aware routing, encrypted overlay networks, LTE/5G failover integration, and centralized policy management across all locations.
Secure cloud on-ramp integration with private connectivity to AWS, Azure, and Google Cloud, ensuring encrypted data flows and low-latency application delivery.
Sabertooth Tech Group helps enterprises in financial services, healthcare, government contracting, and manufacturing implement robust SD-WAN security architectures that combine encrypted overlay networks, zero-trust access controls, and continuous threat monitoring. Leveraging our 300+ partner ecosystem, we source the right combination of SASE platforms, next-gen firewalls, and managed security services to ensure your distributed network infrastructure meets compliance mandates including HIPAA, PCI-DSS, and CMMC while maintaining high performance and operational efficiency.
See how businesses secure their SD-WAN infrastructure with confidence and measurable results.
We simplify SD-WAN security with vendor-agnostic expertise and proven solutions.
Access to leading security vendors ensures you get best-fit solutions for your specific compliance and threat landscape.
Unbiased recommendations driven by your requirements, not vendor commissions or sales quotas.
Deep experience with HIPAA, PCI-DSS, CMMC, and SOC 2 requirements across healthcare, finance, and government sectors.
Single-pane visibility across SASE, zero-trust, EDR, and SIEM platforms for simplified management and faster threat response.
IT security advisors dedicated to protecting your distributed network.
Sabertooth Tech Group has evolved from a consumer-focused AI translation technology company to a comprehensive IT advisory and solution partner serving small and mid-sized businesses across healthcare, legal, financial services, construction, real estate, education, manufacturing, logistics, retail, and government contracting sectors. With a mission to make technology invisible so your business can be unstoppable, we leverage a 300+ partner ecosystem to deliver integrated IT and IoT solutions spanning connectivity, cloud, security, communications, and network infrastructure. Our vision is rooted in removing barriers and expanding possibilities through vendor-agnostic consulting, real-time price benchmarking, and lifecycle management from discovery to deployment and ongoing optimization.
Yes, business continuity planning includes disaster recovery as a critical component. While business continuity focuses on maintaining essential operations during and after a disruptive event, disaster recovery specifically addresses the technical processes and procedures for restoring IT infrastructure, data, and systems. In the context of SD-WAN security, this means implementing redundant network paths, failover mechanisms, encrypted backup connectivity, and documented recovery procedures to ensure network availability and data integrity during security incidents or infrastructure failures.
Talk to our IT security advisors for a free consultation and customized recommendations.
Verified by leading network carriers
Trusted for healthcare data security
Audited security controls and processes
Get a comprehensive security assessment and customized recommendations from our expert IT advisors. We'll respond within one business day.
For immediate assistance, feel free to give us a direct call at +1 888-891-2331
For immediate assistance, feel free to give us a direct call at +1 888-891-2331